Attack synopsis: Credit: Netwrix video. Attack Tutorial: How a Pass the Hash Attack Works
1. Attacker somehow got the password hashes of one or more users on a computer network. If that compromised account has admin rights on that system then that gives the attacker to access other credentials that are stored on the system. Under the sam account database the users password hashes are stored but the file is locked when the system is running so that time it is not possible to access. But operating system still needs that data so they are stored in the memory space of lsass.exe . It can be captured using samdump, pwdump and mimikatz tool and even in offline imaging version of windows.
C:\windows\system32\config\SAM
2. Now using mimikatz tool the attacker leverage compromised users username and password hashes to authenticate other system resources where that user has access to.
Example:
Lets say Jsmith is a normal user account in the domain. He clicked on a phishing mail and his account got compromised. Now attacker have access on his account. But jsmith may not have any rights to access other resources on the domain. However jsmith has local admin rights on his system. Leveraging this, attacker can extract all the password ntlm hashes from the system memory. Say IT admin or domain admin some day, access jsmith computer. So their password hashes are stored already in jsmith's computer system memory. Leveraging jsmith admin rights, attacker can grab those hashes and play pass the hash attack using psexec tool and mimikatz tool.
The user is a part of local administrator group. Not part of any other domain security group.
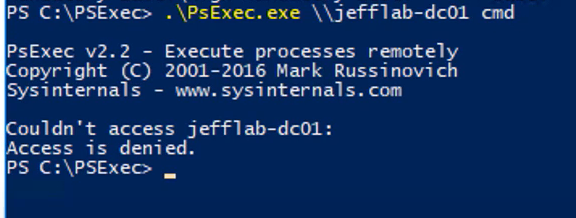
In this case if you want to access your domain controller from this users pc, then you will get access denied message because steveholt does not have that access.
Now lets see how we can elevate our privileges to access the domain controller. The above command will dump out all the password hashes stored in this system.
Now we need to find out a domain administrator account who's account has all rights. We know Tony.WOnder is administrator in our domain environment. So copy his ntlm hash. He may log on to this system to do some work. And his password is stored on the system memory.
Now you just need to pass the hash of tony wonder.
Once you give enter, a new command prompt will be spawned.
In the spawned command prompt when you type whoami, it will still show normal user account which is steveholt. But the elevated token is running behind as part of tony wonder account. So if you use psexec.exe, this time from this shell, you will now have access domain controller with the account of tony wonder.
Image credit: From SANS FOR508 Course.
Using this metasploit psexec, we can also achieve the same.
Avi






Comments
Post a Comment